概览
银行付款方式 (FOP) 是指 Google 与付款集成商(合作伙伴银行或集成商)一次性交换帐号身份凭据和用户授权,以便在 Google 与银行之间建立关联。随后,可将对此关联的引用返回给集成商,以允许将资金从用户帐号转移至其他银行账户。
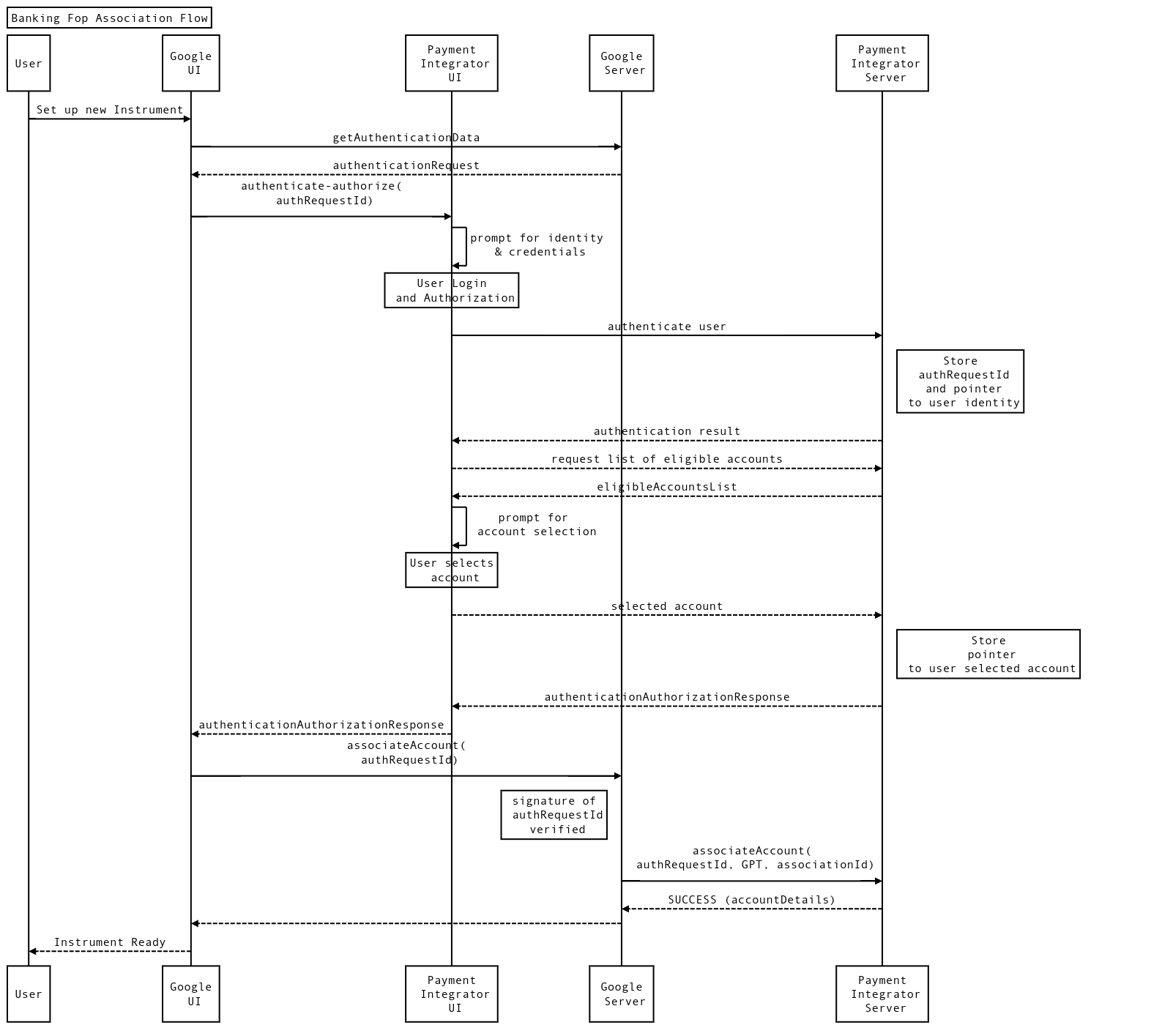
Google 使用两个流程来建立这种信息交换:
- 身份验证授权流程:对用户进行身份验证,并获取用户授权以建立此连接。
- AssociateAccount 流程:为先前识别且经过身份验证的用户建立关联。这可以通过方法调用来实现,该方法会在 Google 与付款集成商之间建立关联。此流程也称为关联。
建立关联后,Google 将在资金转移期间使用该关联,为用户提供快捷顺畅的结账体验。Google 将这种称为插桩。Google 客户有一种或多种付款方式。付款方式是一种在 Google 的各个生态系统和购物平台上为服务和商品付款的方式。
以下各部分更详细地介绍了这些流程。以下部分中的示例将向您介绍一家名为 InvisiBank 的虚构银行。
重要概念
身份验证授权流程
“身份验证-授权”流程的目的是向集成商识别用户身份和进行身份验证,以及获取用户授权以执行流程中的其他操作。身份验证授权通过重定向进行处理。这可以是应用重定向,也可以是网站重定向。
重定向身份验证授权
重定向身份验证授权的发生方式是 Google 将用户重定向到集成商拥有的应用。该应用可以是 Web 应用,也可以是 Android 应用。
Android 重定向和 Web 重定向的行为相似。在这里,Google 会将用户重定向到集成商的应用。集成商以集成商最自然的方式识别用户身份并对用户进行身份验证。通过身份验证后,集成商会将用户重定向回 Google 的界面以完成关联。重定向后,Google 会提供 requestId 以标识此身份验证会话。然后,该标识符在关联期间用作身份验证证明和身份信息。
选择此流程的集成商必须提供网站身份验证网址,因为这是所有平台(桌面设备、移动设备)上的通用标准。不过,强烈建议您使用 Android 身份验证,因为这样可在移动设备上提供最佳用户体验。
根据设备情境和安装的应用,Google 界面会选择 Web 或 Android 应用重定向。
这种身份验证机制为集成商提供了最大的自由度。您可以通过多种方式对用户进行身份验证和识别。用户名 + 密码、生物识别信息和安全问题也是可行的解决方案。Google 并不打算规定集成商验证用户的方式。集成商负责对用户进行身份验证。通过使用此方法,Google 打算利用集成商的各种界面来对用户进行身份验证,而只是向 Google 提供身份验证证明。
此外,我们还将传递一个 Authorization 范围列表,您应向用户显示这些范围,以获取执行上述各项操作的授权(例如,在 AssociateAccount 流程中,我们需要对使用 Google 账号的用户账号进行 associate 授权)。
对于关联流程,此流程还将允许用户在付款集成商处选择自己拥有的帐号,并希望将其作为遵循此流程后的 AssociateAccount 调用的目标。
如需详细了解身份验证,请参阅此详细指南。
关联流程
关联流程旨在建立关联,以便创建付款方式。此流程:
- 在集成商系统中建立关联,将身份验证授权流程中选择的帐号关联到指定的 Google 帐号。
- 协商将用于引用此 Google 付款令牌 (
GPT) 的引用。 - 提供账号信息,以通知 Google 的风险引擎。
已建立的对 GPT 的引用会由 Google 与集成商商定。
关联流程要求 Google 向集成商提供身份验证/授权证明。在每个关联流程之前,Google 都会调用身份验证-授权流程来获取此证明。
下图显示了对身份验证-授权流程和关联流程的调用顺序。
如需详细了解身份验证,请参阅此详细指南。
