O tipo de vinculação OAuth é compatível com dois fluxos do OAuth 2.0 padrão do setor, o implícito e fluxos de código de autorização.
No fluxo de código implícito, o Google abre o endpoint de autorização no navegador do usuário. Após o login, você retorna um token de acesso de longa duração para o Google. Esse token de acesso agora está incluído em todas as solicitações enviadas do Assistente para sua ação.
No fluxo do código de autorização, você precisa de dois endpoints:
- O endpoint de autorização, responsável por apresentar a IU de login aos usuários que ainda não fizeram login e registrar o consentimento para o acesso solicitado na forma de um código de autorização de curta duração.
- O endpoint de troca de token, que é responsável por dois tipos de trocas:
- troca um código de autorização por um token de atualização de longa duração e um token de acesso de curta duração. Essa troca acontece quando o usuário passa pelo fluxo de vinculação da conta.
- Troca um token de atualização de longa duração por um token de acesso de curta duração. Essa troca acontece quando o Google precisa de um novo token de acesso porque ele expirou.
Embora o fluxo do código implícito seja mais simples de implementar, o Google recomenda que os tokens de acesso emitidos usando o fluxo implícito nunca expirem, porque o uso do token com o fluxo implícito força o usuário a vincular a conta novamente. Se você precisar da validade do token por motivos de segurança, considere o uso do fluxo do código de autenticação.
Implementar a vinculação de conta OAuth
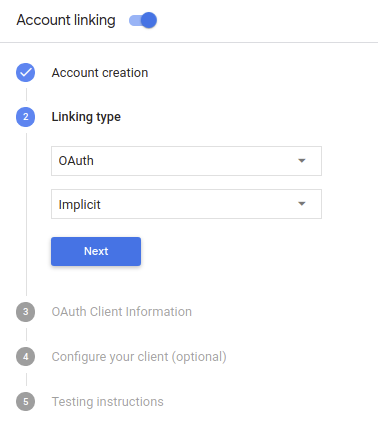
Configurar o projeto
Para configurar seu projeto para usar a vinculação de conta OAuth, siga estas etapas:
- Abra o Console do Actions e selecione o projeto que você quer usar.
- Clique na guia Desenvolver e escolha Vinculação de contas.
- Ative a chave ao lado de Vinculação de contas.
- Na seção Criação de conta, selecione Não, só quero permitir a criação de contas no meu site.
Em Tipo de vinculação, selecione OAuth e Implícito.
Em Informações do cliente:
- Atribua um valor ao ID do cliente emitido pelas suas ações para o Google para identificar solicitações vindas do Google.
- Insira os URLs dos endpoints de autorização e de troca de token.
- Clique em Salvar.
Implementar seu servidor OAuth
Para oferecer suporte ao fluxo implícito do OAuth 2.0, seu serviço faz uma autorização de destino disponível por HTTPS. Esse endpoint é responsável por autenticar e obter consentimento dos usuários para acesso aos dados. O endpoint de autorização apresenta uma interface de login aos usuários que ainda não estão conectados e registra consentir com o acesso solicitado.
Quando seu Action precisa chamar uma das APIs autorizadas do serviço, o Google usa endpoint para obter permissão de seus usuários para chamar essas APIs em seus nome de usuário.
Uma sessão de fluxo implícito do OAuth 2.0 típica iniciada pelo Google tem o seguinte fluxo:
- O Google abre seu endpoint de autorização no navegador do usuário. A o usuário faz login caso ainda não tenha feito isso e concede ao Google permissão para acessar os dados dele com a API, caso ainda não tenham concedido permissão.
- Seu serviço cria um token de acesso e o retorna para o Google redirecionando o navegador do usuário de volta para o Google com o token de acesso; anexada à solicitação.
- O Google chama as APIs do seu serviço e anexa o token de acesso com cada solicitação. O serviço verifica se o token de acesso concede ao Google autorização para acessar a API e, em seguida, conclui a chamada de API.
Processar solicitações de autorização
Quando sua ação precisar vincular a conta usando um fluxo implícito do OAuth2, O Google envia o usuário para seu endpoint de autorização com uma solicitação que inclui os seguintes parâmetros:
| Parâmetros de endpoint de autorização | |
|---|---|
client_id |
O ID do cliente que você atribuiu ao Google. |
redirect_uri |
O URL para o qual você envia a resposta para essa solicitação. |
state |
Um valor de contabilidade que é retornado ao Google inalterado na URI de redirecionamento. |
response_type |
O tipo de valor a ser retornado na resposta. Para a implementação implícita do OAuth 2.0
fluxo, o tipo de resposta será sempre token. |
Por exemplo, se o endpoint de autorização estiver disponível em https://myservice.example.com/auth,
uma solicitação será semelhante a esta:
GET https://myservice.example.com/auth?client_id=GOOGLE_CLIENT_ID&redirect_uri=REDIRECT_URI&state=STATE_STRING&response_type=token
Para que o endpoint de autorização processe solicitações de login, siga estas etapas:
Verifique os valores
client_ideredirect_uripara impedir a concessão de acesso a apps clientes não intencionais ou configurados incorretamente:- Confirme se o
client_idcorresponde ao ID do cliente que você atribuídas ao Google. - Confirme se o URL especificado pelo
redirect_uritem o seguinte formato:https://oauth-redirect.googleusercontent.com/r/YOUR_PROJECT_ID
- Confirme se o
Verifique se o usuário está conectado ao seu serviço. Se o usuário não tiver feito login conclua o fluxo de login ou inscrição do serviço.
Gere um token de acesso que o Google usará para acessar sua API. A token de acesso pode ser qualquer valor de string, mas deve representar exclusivamente o usuário e o cliente a que o token se destina e não pode ser adivinhado.
Envia uma resposta HTTP que redireciona o navegador do usuário para o URL especificado pelo parâmetro
redirect_uri. Inclua todos os elementos parâmetros a seguir no fragmento de URL:access_token: o token de acesso que você acabou de gerar.token_type: a stringbearer.state: o valor do estado não modificado do original. solicitação Veja a seguir um exemplo de URL resultante:https://oauth-redirect.googleusercontent.com/r/YOUR_PROJECT_ID#access_token=ACCESS_TOKEN&token_type=bearer&state=STATE_STRING
O gerenciador de redirecionamento OAuth 2.0 do Google recebe o token de acesso e confirma
que o valor state não mudou. Depois que o Google tiver
token de acesso do seu serviço, o Google o anexa às chamadas subsequentes
à sua ação como parte do AppRequest.
Iniciar o fluxo de autenticação
usar a intent do Assistente de login da conta; para iniciar o fluxo de autenticação. Os snippets de código a seguir descrevem como envie uma resposta no Dialogflow e no SDK do Actions para usar este auxiliar.
Dialogflow:
const {dialogflow, SignIn} = require('actions-on-google'); const app = dialogflow({ // REPLACE THE PLACEHOLDER WITH THE CLIENT_ID OF YOUR ACTIONS PROJECT clientId: CLIENT_ID, }); // Intent that starts the account linking flow. app.intent('Start Signin', (conv) => { conv.ask(new SignIn('To get your account details')); });
@ForIntent("Start Signin") public ActionResponse text(ActionRequest request) { ResponseBuilder rb = getResponseBuilder(request); return rb.add(new SignIn().setContext("To get your account details")).build(); }
{ "payload": { "google": { "expectUserResponse": true, "richResponse": { "items": [ { "simpleResponse": { "textToSpeech": "PLACEHOLDER" } } ] }, "userStorage": "{\"data\":{}}", "systemIntent": { "intent": "actions.intent.SIGN_IN", "data": { "@type": "type.googleapis.com/google.actions.v2.SignInValueSpec", "optContext": "To get your account details" } } } }, "outputContexts": [ { "name": "/contexts/_actions_on_google", "lifespanCount": 99, "parameters": { "data": "{}" } } ] }
SDK do Actions:
const {actionssdk, SignIn} = require('actions-on-google'); const app = actionssdk({ // REPLACE THE PLACEHOLDER WITH THE CLIENT_ID OF YOUR ACTIONS PROJECT clientId: CLIENT_ID, }); // Intent that starts the account linking flow. app.intent('actions.intent.TEXT', (conv) => { conv.ask(new SignIn('To get your account details')); });
@ForIntent("actions.intent.TEXT") public ActionResponse text(ActionRequest request) { ResponseBuilder rb = getResponseBuilder(request); return rb.add(new SignIn().setContext("To get your account details")).build(); }
{ "expectUserResponse": true, "expectedInputs": [ { "inputPrompt": { "richInitialPrompt": { "items": [ { "simpleResponse": { "textToSpeech": "PLACEHOLDER" } } ] } }, "possibleIntents": [ { "intent": "actions.intent.SIGN_IN", "inputValueData": { "@type": "type.googleapis.com/google.actions.v2.SignInValueSpec", "optContext": "To get your account details" } } ] } ], "conversationToken": "{\"data\":{}}", "userStorage": "{\"data\":{}}" }
Processar solicitações de acesso a dados
Se a solicitação do Assistente tiver um token de acesso, faça o seguinte: verifique primeiro se o token de acesso é válido (e não expirado) e, em seguida, recupere a conta de usuário associada do seu banco de dados.