Le type d'association OAuth est compatible avec deux flux OAuth 2.0 standards dans l'industrie : le flux implicite et les flux de code d'autorisation.
Dans le flux de code implicite, Google ouvre votre point de terminaison d'autorisation dans le navigateur de l'utilisateur. Une fois connecté, vous renvoyez un jeton d'accès de longue durée à Google. Ce jeton d'accès est désormais inclus dans chaque requête envoyée à l'action par l'Assistant.
Dans le flux de code d'autorisation, vous avez besoin de deux points de terminaison:
- Le point de terminaison authorization, qui consiste à présenter l'interface de connexion aux utilisateurs qui ne sont pas déjà connectés et à enregistrer le consentement demandé pour l'accès demandé sous la forme d'un code d'autorisation temporaire.
- Le point de terminaison d'échange de jetons, responsable de deux types d'échanges :
- Échange un code d'autorisation contre un jeton d'actualisation de longue durée et un jeton d'accès de courte durée. Cet échange se produit lorsque l'utilisateur suit la procédure d'association de comptes.
- Échange un jeton d'actualisation de longue durée contre un jeton d'accès de courte durée. Cet échange se produit lorsque Google a besoin d'un nouveau jeton d'accès, car celui-ci a expiré.
Bien que le flux de code implicite soit plus facile à mettre en œuvre, Google recommande que les jetons d'accès émis à l'aide du flux implicite n'expirent jamais, car l'expiration du jeton avec le flux implicite oblige l'utilisateur à associer de nouveau son compte. Si vous avez besoin d'un jeton expiré pour des raisons de sécurité, envisagez plutôt d'utiliser le flux de code d'autorisation.
Implémenter l'association de comptes OAuth
Configurer le projet
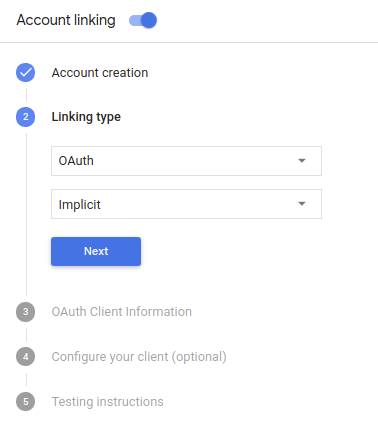
Pour configurer votre projet afin d'utiliser l'association de compte OAuth, procédez comme suit:
- Ouvrez la console Actions et sélectionnez le projet que vous souhaitez utiliser.
- Cliquez sur l'onglet Développer, puis sélectionnez Association de comptes.
- Activez le bouton bascule à côté de l'option Association de comptes.
- Dans la section Création de compte, sélectionnez Non, je souhaite seulement autoriser la création de comptes sur mon site Web.
Dans Type d'association, sélectionnez OAuth et Implicit.
Dans Informations sur le client:
- Attribuez une valeur à Numéro client attribué par le programme Actions à Google pour identifier émanent de Google.
- Insérez les URL de vos points de terminaison Autorisation et Échange de jetons.
- Cliquez sur Enregistrer.
Implémenter votre serveur OAuth
Pour prendre en charge le flux implicite OAuth 2.0, votre service accorde une autorisation un point de terminaison unique disponible via HTTPS. Ce point de terminaison est responsable de l’authentification et l'obtention du consentement des utilisateurs pour l'accès aux données. Le point de terminaison d'autorisation présente une interface utilisateur de connexion aux utilisateurs qui ne sont pas déjà connectés et enregistre autoriser l'accès demandé.
Lorsque votre action doit appeler l'une des API autorisées de votre service, Google utilise ce point de terminaison pour obtenir l'autorisation de vos utilisateurs d'appeler ces API au nom de l'utilisateur.
Une session de flux implicite OAuth 2.0 typique lancée par Google possède le flux suivant:
- Google ouvre votre point de terminaison d'autorisation dans le navigateur de l'utilisateur. La l'utilisateur se connecte s'il n'est pas déjà connecté et autorise Google à y accéder leurs données avec votre API s'ils ne l'ont pas déjà accordé.
- Votre service crée un jeton d'accès et le renvoie à Google en redirigeant le navigateur de l'utilisateur vers Google à l'aide du jeton d'accès joint à la demande.
- Google appelle les API de votre service et associe le jeton d'accès chaque requête. Votre service vérifie que le jeton d'accès accorde à Google l'autorisation d'accès à l'API, puis termine l'appel d'API.
Gérer les requêtes d'autorisation
Lorsque votre action doit associer des comptes via un flux implicite OAuth2, Google renvoie l'utilisateur vers votre point de terminaison d'autorisation avec une requête qui inclut les paramètres suivants:
| Paramètres du point de terminaison de l'autorisation | |
|---|---|
client_id |
ID client que vous avez attribué à Google. |
redirect_uri |
URL à laquelle vous envoyez la réponse à cette requête. |
state |
Une valeur de tenue de registre renvoyée à Google telle quelle dans le l'URI de redirection. |
response_type |
Type de valeur à renvoyer dans la réponse. Pour l'authentification OAuth 2.0
le type de réponse est toujours token. |
Par exemple, si votre point de terminaison d'autorisation est disponible à l'adresse https://myservice.example.com/auth,
une requête peut se présenter comme suit:
GET https://myservice.example.com/auth?client_id=GOOGLE_CLIENT_ID&redirect_uri=REDIRECT_URI&state=STATE_STRING&response_type=token
Pour que votre point de terminaison d'autorisation traite les requêtes de connexion, procédez comme suit:
Vérifiez les valeurs
client_idetredirect_uripour pour empêcher l'octroi d'accès à des applications clientes non intentionnelles ou mal configurées:- Vérifiez que
client_idcorrespond à l'ID client que vous attribué à Google. - Vérifiez que l'URL spécifiée par
redirect_uria la forme suivante:https://oauth-redirect.googleusercontent.com/r/YOUR_PROJECT_ID
- Vérifiez que
Vérifiez si l'utilisateur est connecté à votre service. Si l'utilisateur n'est pas signé suivez la procédure de connexion ou d'inscription de votre service.
Générez un jeton d'accès que Google utilisera pour accéder à votre API. La Le jeton d'accès peut correspondre à n'importe quelle valeur de chaîne, mais il doit représenter de manière unique le user et le client pour lequel le jeton est destiné et ne doit pas être devinable.
Envoyer une réponse HTTP qui redirige le navigateur de l'utilisateur vers l'URL spécifiée par le paramètre
redirect_uri. Incluez tous les les paramètres suivants dans le fragment d'URL:access_token: jeton d'accès que vous venez de générertoken_type: chaînebearerstate: valeur de l'état non modifié de l'original demander Voici un exemple de l'URL obtenue:https://oauth-redirect.googleusercontent.com/r/YOUR_PROJECT_ID#access_token=ACCESS_TOKEN&token_type=bearer&state=STATE_STRING
Le gestionnaire de redirection OAuth 2.0 de Google recevra le jeton d'accès et confirmera
que la valeur state n'a pas changé. Une fois que Google a obtenu
pour votre service, Google l'associe aux appels suivants
à votre action dans le cadre de AppRequest.
Démarrer le flux d'authentification
Utiliser l'intent d'assistance à la connexion au compte pour démarrer le flux d'authentification. Les extraits de code suivants décrivent comment envoyer une réponse dans Dialogflow et le SDK Actions pour utiliser cet outil d'aide.
Dialogflow:
<ph type="x-smartling-placeholder">const {dialogflow, SignIn} = require('actions-on-google'); const app = dialogflow({ // REPLACE THE PLACEHOLDER WITH THE CLIENT_ID OF YOUR ACTIONS PROJECT clientId: CLIENT_ID, }); // Intent that starts the account linking flow. app.intent('Start Signin', (conv) => { conv.ask(new SignIn('To get your account details')); });
@ForIntent("Start Signin") public ActionResponse text(ActionRequest request) { ResponseBuilder rb = getResponseBuilder(request); return rb.add(new SignIn().setContext("To get your account details")).build(); }
{ "payload": { "google": { "expectUserResponse": true, "richResponse": { "items": [ { "simpleResponse": { "textToSpeech": "PLACEHOLDER" } } ] }, "userStorage": "{\"data\":{}}", "systemIntent": { "intent": "actions.intent.SIGN_IN", "data": { "@type": "type.googleapis.com/google.actions.v2.SignInValueSpec", "optContext": "To get your account details" } } } }, "outputContexts": [ { "name": "/contexts/_actions_on_google", "lifespanCount": 99, "parameters": { "data": "{}" } } ] }
SDK Actions:
<ph type="x-smartling-placeholder">const {actionssdk, SignIn} = require('actions-on-google'); const app = actionssdk({ // REPLACE THE PLACEHOLDER WITH THE CLIENT_ID OF YOUR ACTIONS PROJECT clientId: CLIENT_ID, }); // Intent that starts the account linking flow. app.intent('actions.intent.TEXT', (conv) => { conv.ask(new SignIn('To get your account details')); });
@ForIntent("actions.intent.TEXT") public ActionResponse text(ActionRequest request) { ResponseBuilder rb = getResponseBuilder(request); return rb.add(new SignIn().setContext("To get your account details")).build(); }
{ "expectUserResponse": true, "expectedInputs": [ { "inputPrompt": { "richInitialPrompt": { "items": [ { "simpleResponse": { "textToSpeech": "PLACEHOLDER" } } ] } }, "possibleIntents": [ { "intent": "actions.intent.SIGN_IN", "inputValueData": { "@type": "type.googleapis.com/google.actions.v2.SignInValueSpec", "optContext": "To get your account details" } } ] } ], "conversationToken": "{\"data\":{}}", "userStorage": "{\"data\":{}}" }
Gérer les requêtes d'accès aux données
Si la requête Assistant contient un jeton d'accès, commencez par vérifier que le jeton d'accès est valide (et qu'il n'a pas expiré), puis récupérez le compte utilisateur associé dans votre base de données.

