نظرة عامة
تضيف ميزة الربط المُبسَّط لميزة "تسجيل الدخول باستخدام حساب Google" المستندة إلى OAuth ميزة "تسجيل الدخول باستخدام حساب Google" إلى ربط OAuth. يقدّم ذلك تجربة ربط سلسة لمستخدمي Google، كما يتيح إنشاء الحسابات، ما يسمح للمستخدم بإنشاء حساب جديد على خدمتك باستخدام حسابه على Google.
لإجراء عملية ربط الحساب باستخدام بروتوكول OAuth وميزة "تسجيل الدخول باستخدام حساب Google"، اتّبِع الخطوات العامة التالية:
- أولاً، اطلب من المستخدم الموافقة على الوصول إلى ملفه الشخصي على Google.
- استخدِم المعلومات الواردة في ملفه الشخصي للتحقّق مما إذا كان حساب المستخدم متوفّرًا.
- بالنسبة إلى المستخدمين الحاليين، عليك ربط الحسابات.
- إذا لم تتمكّن من العثور على مطابقة لمستخدم Google في نظام المصادقة، عليك التحقّق من صحة الرمز المميّز للهوية الذي تم تلقّيه من Google. يمكنك بعد ذلك إنشاء مستخدم استنادًا إلى معلومات الملف الشخصي الواردة في رمز التعريف.
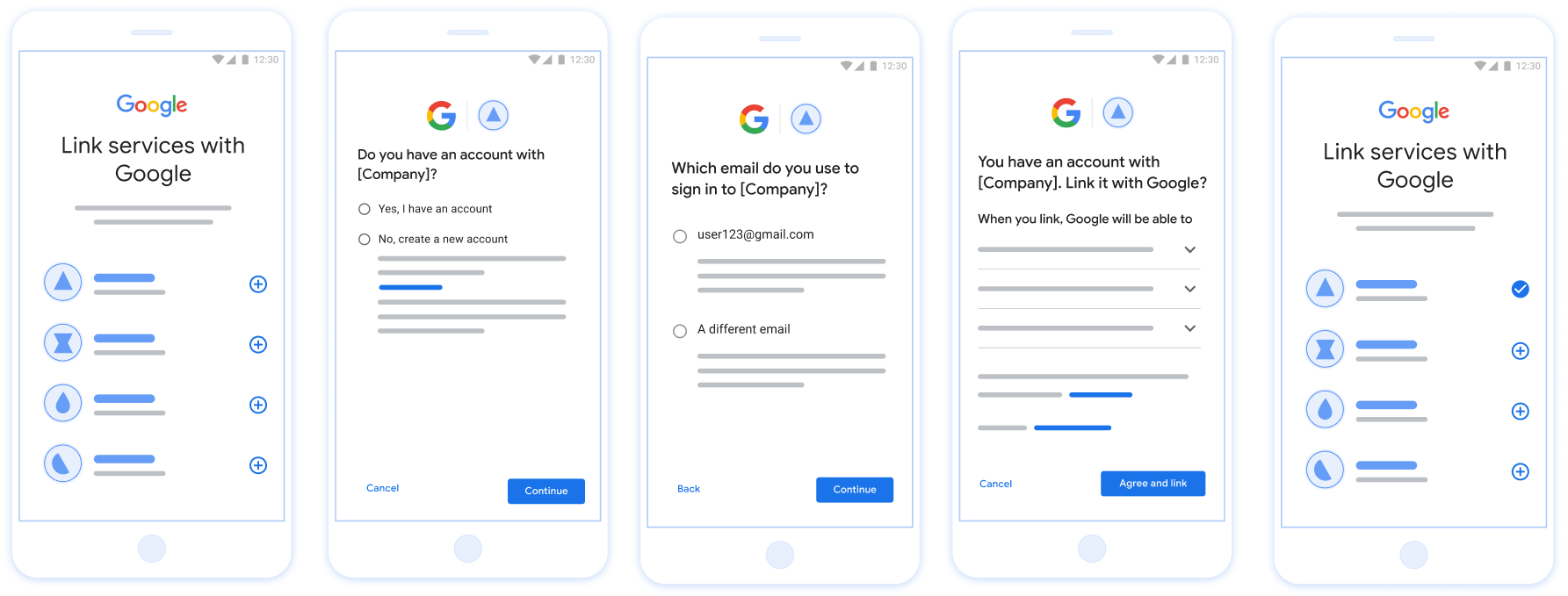
الشكل 1: ربط الحساب على هاتف المستخدم باستخدام ميزة "الربط الميسّر"
متطلبات ميزة "الربط الميسّر"
- نفِّذ خطوات الربط الأساسي عبر بروتوكول OAuth على الويب. يجب أن تتوافق خدمتك مع نقاط نهاية التفويض واستبدال الرموز المميَّزة المتوافقة مع OAuth 2.0.
- يجب أن تتيح نقطة نهاية تبادل الرموز المميّزة رموز JSON المميّزة للويب (JWT) وتنفيذ النية
checkوcreateوget.
تنفيذ خادم OAuth
يجب أن تتيح نقطة نهاية تبادل الرموز المميّزة نوايا check وcreate وget. يوضّح الجدول أدناه الخطوات التي تم إكمالها خلال عملية ربط الحساب ويشير إلى وقت استدعاء النوايا المختلفة:
- هل لدى المستخدم حساب في نظام المصادقة؟ (يحدد المستخدم ذلك من خلال اختيار "نعم" أو "لا")
- نعم : هل يستخدم المستخدم عنوان البريد الإلكتروني المرتبط بحسابه على Google لتسجيل الدخول إلى منصتك؟ (يحدد المستخدم ذلك عن طريق اختيار "نعم" أو "لا")
- نعم : هل لدى المستخدم حساب مطابق في نظام المصادقة؟ (يتم الاتصال بالرقم
check intentللتأكيد)- نعم : يتمّ استدعاء
get intentويتمّ ربط الحساب إذا تمّ عرض النيّة بنجاح. - لا، هل تريد إنشاء حساب جديد؟ (يحدد المستخدم ذلك عن طريق اختيار "نعم" أو "لا")
- نعم : يتمّ استدعاء
create intentويتمّ ربط الحساب إذا تمّ عرض نية الإنشاء بنجاح. - لا : يتم بدء عملية Web OAuth، ويتم توجيه المستخدم إلى المتصفّح، ويتم منح المستخدم خيار الربط ببريد إلكتروني مختلف.
- نعم : يتمّ استدعاء
- نعم : يتمّ استدعاء
- لا : يتم تفعيل مسار Web OAuth، ويتم توجيه المستخدم إلى المتصفّح، ويتم منح المستخدم خيار الربط ببريد إلكتروني مختلف.
- نعم : هل لدى المستخدم حساب مطابق في نظام المصادقة؟ (يتم الاتصال بالرقم
- لا : هل لدى المستخدم حساب مطابق في نظام المصادقة؟ (يتم الاتصال بالرقم
check intentللتأكيد)- نعم : يتمّ استدعاء
get intentويتمّ ربط الحساب إذا تمّ عرض النيّة بنجاح. - لا : يتمّ استدعاء
create intentويتمّ ربط الحساب إذا تمّ عرض نية الإنشاء بنجاح.
- نعم : يتمّ استدعاء
- نعم : هل يستخدم المستخدم عنوان البريد الإلكتروني المرتبط بحسابه على Google لتسجيل الدخول إلى منصتك؟ (يحدد المستخدم ذلك عن طريق اختيار "نعم" أو "لا")
التحقّق من توفّر حساب مستخدم حالي (التحقّق من النية)
بعد أن يمنح المستخدِم موافقته على الوصول إلى ملفه الشخصي في Google، ترسل Google طلب يتضمن تأكيدًا موقَّعًا على هوية مستخدم Google. تشير رسالة الأشكال البيانية يحتوي تأكيد البيانات على معلومات تشتمل على رقم تعريف حساب المستخدم على Google، والاسم وعنوان البريد الإلكتروني. نقطة نهاية تبادل الرموز المميّزة التي تم ضبطها المشروع أن يتعامل مع هذا الطلب.
في حال توفُّر حساب Google المناسب في المصادقة
فإن نقطة نهاية تبادل الرمز المميز تستجيب باستخدام account_found=true. إذا كانت
لا يتطابق حساب Google مع مستخدم حالي، نقطة نهاية تبادل الرموز المميّزة
تعرض الخطأ HTTP 404 لم يتم العثور على الصفحة مع account_found=false.
يكون الطلب بالشكل التالي:
POST /token HTTP/1.1 Host: oauth2.example.com Content-Type: application/x-www-form-urlencoded grant_type=urn:ietf:params:oauth:grant-type:jwt-bearer&intent=check&assertion=JWT&scope=SCOPES&client_id=GOOGLE_CLIENT_ID&client_secret=GOOGLE_CLIENT_SECRET
يجب أن تتمكّن نقطة نهاية تبادل الرموز المميّزة من معالجة المَعلمات التالية:
| مَعلمات نقطة نهاية الرمز المميّز | |
|---|---|
intent |
بالنسبة إلى هذه الطلبات، تكون قيمة هذه المعلمة
check |
grant_type |
تمثّل هذه السمة نوع الرمز المميّز الذي يتم تبادله. بالنسبة لهذه الطلبات، سيتم
المعلَمة urn:ietf:params:oauth:grant-type:jwt-bearer. |
assertion |
يشير هذا المصطلح إلى رمز JSON المميّز للويب (JWT) ويقدِّم تأكيدًا موقَّعًا على بيانات وهوية المستخدم. يحتوي JWT على معلومات تتضمن عنوان URL الخاص رقم تعريف حساب Google والاسم وعنوان البريد الإلكتروني |
client_id |
معرِّف العميل الذي عيّنته لـ Google. |
client_secret |
سر العميل الذي خصّصته لـ Google. |
للردّ على طلبات intent لـ check، يجب أن تنفِّذ نقطة نهاية تبادل الرموز المميّزة الخطوات التالية:
- التحقق من صحة تأكيد JWT وفك ترميزه
- تحقَّق مما إذا كان حساب Google متوفّرًا من قبل في نظام المصادقة.
التحقق من صحة تأكيد JWT وفك ترميزه
يمكنك التحقق من صحة تأكيد JWT وفك ترميزه باستخدام مكتبة فك ترميز JWT بلغتك. استخدام مفاتيح Google العامة، متاحة في JWK أو PEM، للتأكّد من توقيع الرمز المميز.
عند فك ترميز النص، يظهر تأكيد JWT على النحو التالي:
{ "sub": "1234567890", // The unique ID of the user's Google Account "iss": "https://accounts.google.com", // The assertion's issuer "aud": "123-abc.apps.googleusercontent.com", // Your server's client ID "iat": 233366400, // Unix timestamp of the assertion's creation time "exp": 233370000, // Unix timestamp of the assertion's expiration time "name": "Jan Jansen", "given_name": "Jan", "family_name": "Jansen", "email": "jan@gmail.com", // If present, the user's email address "email_verified": true, // true, if Google has verified the email address "hd": "example.com", // If present, the host domain of the user's GSuite email address // If present, a URL to user's profile picture "picture": "https://lh3.googleusercontent.com/a-/AOh14GjlTnZKHAeb94A-FmEbwZv7uJD986VOF1mJGb2YYQ", "locale": "en_US" // User's locale, from browser or phone settings }
بالإضافة إلى التحقّق من توقيع الرمز المميّز، تأكَّد من أنّ التأكيد
جهة الإصدار (الحقل iss) هي https://accounts.google.com، بحيث يمكن لشريحة الجمهور
(الحقل aud) هو معرّف العميل الذي تم تعيينه، ولم تنتهِ صلاحية الرمز المميّز.
(حقل exp).
باستخدام الحقول email وemail_verified وhd، يمكنك تحديد ما إذا كان
تستضيف Google عناوين البريد الإلكتروني وموثوقًا بها. في الحالات التي تواجه فيها Google
موثوقية المستخدم المعروف حاليًا بأنه صاحب الحساب الشرعي
ويمكنك تخطي كلمة المرور أو طرق التحديات الأخرى. بخلاف ذلك، فإن هذه الطرق
يمكن استخدامها للتحقّق من الحساب قبل ربطه
الحالات التي تكون فيها Google موثوقة:
- السمة
emailهي اللاحقة@gmail.com، وهذا حساب Gmail. email_verifiedصحيح وتم ضبطhd، هذا حساب G Suite.
يمكن للمستخدمين التسجيل للحصول على حسابات Google بدون استخدام Gmail أو G Suite. فعندما
لا يحتوي email على اللاحقة @gmail.com وhd غير موجود في Google
موثوقة وكلمة المرور أو طرق التحقق الأخرى للتحقق
المستخدم. يمكن أن يكون email_verified صحيحًا أيضًا لأن Google تحققت في البداية من صحة
المستخدم عند إنشاء حساب Google، ولكن ملكية الجهة الخارجية
ربما تغير حساب بريدك الإلكتروني منذ ذلك الحين.
التأكّد من توفّر حساب Google في نظام المصادقة
تحقق مما إذا كان أي من الشروط التالية صحيحًا:
- رقم تعريف حساب Google، الوارد في حقل
subفي التأكيد، موجود في حساب المستخدم. قاعدة البيانات. - يتطابق عنوان البريد الإلكتروني الوارد في التأكيد مع مستخدم في قاعدة بيانات المستخدم الخاصة بك.
في حال استيفاء أيٌّ من الشروط، يعني هذا أنّ المستخدم قد اشترك في الخدمة من قبل. في هذه الحالة، إرجاع رد مثل ما يلي:
HTTP/1.1 200 Success
Content-Type: application/json;charset=UTF-8
{
"account_found":"true",
}
إذا لم يكن معرّف حساب Google أو عنوان البريد الإلكتروني المحددَين في
تطابق تأكيد مع مستخدم في قاعدة البيانات الخاصة بك، لم يشترك المستخدم بعد. ضِمن
في هذه الحالة، تحتاج نقطة نهاية تبادل الرمز المميّز إلى الردّ مع عرض خطأ HTTP 404
تحدّد هذه السمة "account_found": "false"، كما في المثال التالي:
HTTP/1.1 404 Not found
Content-Type: application/json;charset=UTF-8
{
"account_found":"false",
}
التعامل مع الربط التلقائي (تحقيق النية)
بعد أن يمنح المستخدِم موافقته على الوصول إلى ملفه الشخصي في Google، ترسل Google طلب يتضمن تأكيدًا موقَّعًا على هوية مستخدم Google. تشير رسالة الأشكال البيانية يحتوي تأكيد البيانات على معلومات تشتمل على رقم تعريف حساب المستخدم على Google، والاسم وعنوان البريد الإلكتروني. نقطة نهاية تبادل الرموز المميّزة التي تم ضبطها المشروع أن يتعامل مع هذا الطلب.
في حال توفُّر حساب Google المناسب في المصادقة
فإن نقطة نهاية تبادل الرمز المميز تقوم بإرجاع رمز مميز للمستخدم. إذا كانت
لا يتطابق حساب Google مع مستخدم حالي، نقطة نهاية تبادل الرموز المميّزة
تعرض الخطأ linking_error وعرض login_hint اختياري.
يكون الطلب بالشكل التالي:
POST /token HTTP/1.1 Host: oauth2.example.com Content-Type: application/x-www-form-urlencoded grant_type=urn:ietf:params:oauth:grant-type:jwt-bearer&intent=get&assertion=JWT&scope=SCOPES&client_id=GOOGLE_CLIENT_ID&client_secret=GOOGLE_CLIENT_SECRET
يجب أن تتمكّن نقطة نهاية تبادل الرموز المميّزة من معالجة المَعلمات التالية:
| مَعلمات نقطة نهاية الرمز المميّز | |
|---|---|
intent |
بالنسبة إلى هذه الطلبات، تكون قيمة هذه المَعلمة هي get. |
grant_type |
تمثّل هذه السمة نوع الرمز المميّز الذي يتم تبادله. بالنسبة لهذه الطلبات، سيتم
المعلَمة urn:ietf:params:oauth:grant-type:jwt-bearer. |
assertion |
يشير هذا المصطلح إلى رمز JSON المميّز للويب (JWT) ويقدِّم تأكيدًا موقَّعًا على بيانات وهوية المستخدم. يحتوي JWT على معلومات تتضمن عنوان URL الخاص رقم تعريف حساب Google والاسم وعنوان البريد الإلكتروني |
scope |
اختياري: أي نطاقات تم ضبط Google فيها للطلب منها المستخدمين. |
client_id |
معرِّف العميل الذي عيّنته لـ Google. |
client_secret |
سر العميل الذي خصّصته لـ Google. |
للردّ على طلبات intent لـ get، يجب أن تنفِّذ نقطة نهاية تبادل الرموز المميّزة الخطوات التالية:
- التحقق من صحة تأكيد JWT وفك ترميزه
- تحقَّق مما إذا كان حساب Google متوفّرًا من قبل في نظام المصادقة.
التحقق من صحة تأكيد JWT وفك ترميزه
يمكنك التحقق من صحة تأكيد JWT وفك ترميزه باستخدام مكتبة فك ترميز JWT بلغتك. استخدام مفاتيح Google العامة، متاحة في JWK أو PEM، للتأكّد من توقيع الرمز المميز.
عند فك ترميز النص، يظهر تأكيد JWT على النحو التالي:
{ "sub": "1234567890", // The unique ID of the user's Google Account "iss": "https://accounts.google.com", // The assertion's issuer "aud": "123-abc.apps.googleusercontent.com", // Your server's client ID "iat": 233366400, // Unix timestamp of the assertion's creation time "exp": 233370000, // Unix timestamp of the assertion's expiration time "name": "Jan Jansen", "given_name": "Jan", "family_name": "Jansen", "email": "jan@gmail.com", // If present, the user's email address "email_verified": true, // true, if Google has verified the email address "hd": "example.com", // If present, the host domain of the user's GSuite email address // If present, a URL to user's profile picture "picture": "https://lh3.googleusercontent.com/a-/AOh14GjlTnZKHAeb94A-FmEbwZv7uJD986VOF1mJGb2YYQ", "locale": "en_US" // User's locale, from browser or phone settings }
بالإضافة إلى التحقّق من توقيع الرمز المميّز، تأكَّد من أنّ التأكيد
جهة الإصدار (الحقل iss) هي https://accounts.google.com، بحيث يمكن لشريحة الجمهور
(الحقل aud) هو معرّف العميل الذي تم تعيينه، ولم تنتهِ صلاحية الرمز المميّز.
(حقل exp).
باستخدام الحقول email وemail_verified وhd، يمكنك تحديد ما إذا كان
تستضيف Google عناوين البريد الإلكتروني وموثوقًا بها. في الحالات التي تواجه فيها Google
موثوقية المستخدم المعروف حاليًا بأنه صاحب الحساب الشرعي
ويمكنك تخطي كلمة المرور أو طرق التحديات الأخرى. بخلاف ذلك، فإن هذه الطرق
يمكن استخدامها للتحقّق من الحساب قبل ربطه
الحالات التي تكون فيها Google موثوقة:
- السمة
emailهي اللاحقة@gmail.com، وهذا حساب Gmail. email_verifiedصحيح وتم ضبطhd، هذا حساب G Suite.
يمكن للمستخدمين التسجيل للحصول على حسابات Google بدون استخدام Gmail أو G Suite. فعندما
لا يحتوي email على اللاحقة @gmail.com وhd غير موجود في Google
موثوقة وكلمة المرور أو طرق التحقق الأخرى للتحقق
المستخدم. يمكن أن يكون email_verified صحيحًا أيضًا لأن Google تحققت في البداية من صحة
المستخدم عند إنشاء حساب Google، ولكن ملكية الجهة الخارجية
ربما تغير حساب بريدك الإلكتروني منذ ذلك الحين.
التأكّد من توفّر حساب Google في نظام المصادقة
تحقق مما إذا كان أي من الشروط التالية صحيحًا:
- رقم تعريف حساب Google، الوارد في حقل
subفي التأكيد، موجود في حساب المستخدم. قاعدة البيانات. - يتطابق عنوان البريد الإلكتروني الوارد في التأكيد مع مستخدم في قاعدة بيانات المستخدم الخاصة بك.
في حال العثور على حساب للمستخدم، عليك إصدار رمز دخول وعرض القيم في كائن JSON في نص استجابة HTTPS، كما في المثال التالي:
{ "token_type": "Bearer", "access_token": "ACCESS_TOKEN", "refresh_token": "REFRESH_TOKEN", "expires_in": SECONDS_TO_EXPIRATION }
في بعض الحالات، قد يتعذّر على المستخدم ربط الحساب استنادًا إلى الرمز المميّز للمعرّف. إذا كان
لأي سبب من الأسباب، تحتاج نقطة نهاية تبادل الرمز المميز إلى الرد باستخدام HTTP
401 يحدد الخطأ error=linking_error، كما يبيِّن المثال التالي:
HTTP/1.1 401 Unauthorized
Content-Type: application/json;charset=UTF-8
{
"error":"linking_error",
"login_hint":"foo@bar.com"
}
عندما تتلقّى Google ردًّا بالخطأ 401 مع linking_error، ترسل Google
المستخدِم إلى نقطة نهاية التفويض مع استخدام login_hint كمَعلمة. تشير رسالة الأشكال البيانية
إكمال المستخدم لربط الحساب باستخدام مسار ربط OAuth في المتصفِّح
معالجة عملية إنشاء الحساب من خلال تسجيل الدخول بحساب Google (إنشاء هدف)
عندما يحتاج مستخدم إلى إنشاء حساب على خدمتك، تقدِّم Google طلبًا.
إلى نقطة نهاية تبادل الرمز المميّز التي تحدّد intent=create.
يكون الطلب بالشكل التالي:
POST /token HTTP/1.1 Host: oauth2.example.com Content-Type: application/x-www-form-urlencoded response_type=token&grant_type=urn:ietf:params:oauth:grant-type:jwt-bearer&scope=SCOPES&intent=create&assertion=JWT&client_id=GOOGLE_CLIENT_ID&client_secret=GOOGLE_CLIENT_SECRET
يجب أن تتمكّن نقطة نهاية تبادل الرموز المميّزة من معالجة المَعلمات التالية:
| مَعلمات نقطة نهاية الرمز المميّز | |
|---|---|
intent |
بالنسبة إلى هذه الطلبات، تكون قيمة هذه المَعلمة هي create. |
grant_type |
تمثّل هذه السمة نوع الرمز المميّز الذي يتم تبادله. بالنسبة لهذه الطلبات، سيتم
المعلَمة urn:ietf:params:oauth:grant-type:jwt-bearer. |
assertion |
يشير هذا المصطلح إلى رمز JSON المميّز للويب (JWT) ويقدِّم تأكيدًا موقَّعًا على بيانات وهوية المستخدم. يحتوي JWT على معلومات تتضمن عنوان URL الخاص رقم تعريف حساب Google والاسم وعنوان البريد الإلكتروني |
client_id |
معرِّف العميل الذي عيّنته لـ Google. |
client_secret |
سر العميل الذي خصّصته لـ Google. |
إنّ JWT ضمن المَعلمة assertion يحتوي على رقم تعريف حساب Google للمستخدِم.
والاسم وعنوان البريد الإلكتروني، اللذين يمكنك استخدامهما لإنشاء حساب جديد على
خدمة ما.
للردّ على طلبات intent لـ create، يجب أن تنفِّذ نقطة نهاية تبادل الرموز المميّزة الخطوات التالية:
- التحقق من صحة تأكيد JWT وفك ترميزه
- تحقَّق من صحة معلومات المستخدم وأنشئ حسابًا جديدًا.
التحقق من صحة تأكيد JWT وفك ترميزه
يمكنك التحقق من صحة تأكيد JWT وفك ترميزه باستخدام مكتبة فك ترميز JWT بلغتك. استخدام مفاتيح Google العامة، متاحة في JWK أو PEM، للتأكّد من توقيع الرمز المميز.
عند فك ترميز النص، يظهر تأكيد JWT على النحو التالي:
{ "sub": "1234567890", // The unique ID of the user's Google Account "iss": "https://accounts.google.com", // The assertion's issuer "aud": "123-abc.apps.googleusercontent.com", // Your server's client ID "iat": 233366400, // Unix timestamp of the assertion's creation time "exp": 233370000, // Unix timestamp of the assertion's expiration time "name": "Jan Jansen", "given_name": "Jan", "family_name": "Jansen", "email": "jan@gmail.com", // If present, the user's email address "email_verified": true, // true, if Google has verified the email address "hd": "example.com", // If present, the host domain of the user's GSuite email address // If present, a URL to user's profile picture "picture": "https://lh3.googleusercontent.com/a-/AOh14GjlTnZKHAeb94A-FmEbwZv7uJD986VOF1mJGb2YYQ", "locale": "en_US" // User's locale, from browser or phone settings }
بالإضافة إلى التحقّق من توقيع الرمز المميّز، تأكَّد من أنّ التأكيد
جهة الإصدار (الحقل iss) هي https://accounts.google.com، بحيث يمكن لشريحة الجمهور
(الحقل aud) هو معرّف العميل الذي تم تعيينه، ولم تنتهِ صلاحية الرمز المميّز.
(حقل exp).
باستخدام الحقول email وemail_verified وhd، يمكنك تحديد ما إذا كان
تستضيف Google عناوين البريد الإلكتروني وموثوقًا بها. في الحالات التي تواجه فيها Google
موثوقية المستخدم المعروف حاليًا بأنه صاحب الحساب الشرعي
ويمكنك تخطي كلمة المرور أو طرق التحديات الأخرى. بخلاف ذلك، فإن هذه الطرق
يمكن استخدامها للتحقّق من الحساب قبل ربطه
الحالات التي تكون فيها Google موثوقة:
- السمة
emailهي اللاحقة@gmail.com، وهذا حساب Gmail. email_verifiedصحيح وتم ضبطhd، هذا حساب G Suite.
يمكن للمستخدمين التسجيل للحصول على حسابات Google بدون استخدام Gmail أو G Suite. فعندما
لا يحتوي email على اللاحقة @gmail.com وhd غير موجود في Google
موثوقة وكلمة المرور أو طرق التحقق الأخرى للتحقق
المستخدم. يمكن أن يكون email_verified صحيحًا أيضًا لأن Google تحققت في البداية من صحة
المستخدم عند إنشاء حساب Google، ولكن ملكية الجهة الخارجية
ربما تغير حساب بريدك الإلكتروني منذ ذلك الحين.
التحقق من صحة معلومات المستخدم وإنشاء حساب جديد
تحقق مما إذا كان أي من الشروط التالية صحيحًا:
- رقم تعريف حساب Google، الوارد في حقل
subفي التأكيد، موجود في حساب المستخدم. قاعدة البيانات. - يتطابق عنوان البريد الإلكتروني الوارد في التأكيد مع مستخدم في قاعدة بيانات المستخدم الخاصة بك.
في حال استيفاء أيٌّ من الشروط، اطلب من المستخدم ربط حسابه الحالي.
باستخدام حساباتهم على Google. ولإجراء ذلك، استجب للطلب برسالة الخطأ HTTP 401
التي تحدّد error=linking_error وتمنح عنوان البريد الإلكتروني للمستخدم
login_hint فيما يلي نموذج للرد:
HTTP/1.1 401 Unauthorized
Content-Type: application/json;charset=UTF-8
{
"error":"linking_error",
"login_hint":"foo@bar.com"
}
عندما تتلقّى Google ردًّا بالخطأ 401 مع linking_error، ترسل Google
المستخدِم إلى نقطة نهاية التفويض مع استخدام login_hint كمَعلمة. تشير رسالة الأشكال البيانية
إكمال المستخدم لربط الحساب باستخدام مسار ربط OAuth في المتصفِّح
إذا لم يكن أي من الشرطين صحيحًا، عليك إنشاء حساب مستخدم جديد باستخدام المعلومات. المقدمة في JWT. لا يتم عادةً ضبط كلمة مرور للحسابات الجديدة. من المهم ننصح بإضافة حساب Google إلى المنصات الأخرى ليتمكّن المستخدمون من سجِّل الدخول باستخدام حساب Google على مختلف مساحات عرض تطبيقك. بدلاً من ذلك، يمكنك إرسال رسالة إلكترونية إلى المستخدم تتضمن رابطًا يبدأ مسار استرداد كلمة المرور للسماح المستخدم بتعيين كلمة مرور لتسجيل الدخول على أنظمة أساسية أخرى.
عند اكتمال الإنشاء، يمكنك إصدار رمز دخول وعرض القيم في كائن JSON نص استجابة HTTPS، كما في المثال التالي:
{ "token_type": "Bearer", "access_token": "ACCESS_TOKEN", "refresh_token": "REFRESH_TOKEN", "expires_in": SECONDS_TO_EXPIRATION }
الحصول على معرّف عميل Google API
سيُطلب منك تقديم معرّف عميل Google API أثناء عملية تسجيل ميزة "ربط الحساب".
للحصول على معرِّف عميل واجهة برمجة التطبيقات باستخدام المشروع الذي أنشأته أثناء إكمال خطوات ربط OAuth. لإجراء ذلك، يُرجى إكمال الخطوات التالية:
أنشئ مشروعًا على Google APIs أو اختَره.
إذا لم يكن مشروعك يتضمّن معرّف عميل لنوع تطبيق الويب، انقر على إنشاء عميل لإنشاء معرّف. احرص على تضمين نطاق موقعك الإلكتروني في مربّع مصادر JavaScript المسموح بها. عند إجراء اختبارات محلية أو تطوير، يجب إضافة كل من
http://localhostوhttp://localhost:<port_number>إلى حقل مصادر JavaScript المعتمَدة.
التحقّق من صحة عملية التنفيذ
يمكنك التحقّق من صحة التنفيذ باستخدام أداة ساحة اختبار OAuth 2.0.
في الأداة، اتّبِع الخطوات التالية:
- انقر على رمز الإعدادات لفتح نافذة ضبط OAuth 2.0.
- في حقل مسار OAuth، اختَر جانب العميل.
- في الحقل نقاط نهاية OAuth، اختَر مخصّص.
- حدِّد نقطة نهاية OAuth 2.0 ومعرّف العميل الذي عيّنته لخدمة Google في الحقول المقابلة.
- في قسم الخطوة 1، لا تختَر أيّ نطاقات Google. بدلاً من ذلك، اترك هذا الحقل فارغًا أو اكتب نطاقًا صالحًا لخادمك (أو سلسلة عشوائية إذا كنت لا تستخدم نطاقات OAuth). عند الانتهاء، انقر على تفويض واجهات برمجة التطبيقات.
- في القسمَين الخطوة 2 والخطوة 3، انتقِل إلى مسار OAuth 2.0 وتحقَّق من أنّ كل خطوة تعمل على النحو المطلوب.
يمكنك التحقّق من صحة عملية التنفيذ باستخدام أداة العرض التوضيحي لربط حساب Google.
في الأداة، اتّبِع الخطوات التالية:
- انقر على الزر تسجيل الدخول باستخدام حساب Google.
- اختَر الحساب الذي تريد ربطه.
- أدخِل رقم تعريف الخدمة.
- يمكنك اختياريًا إدخال نطاق واحد أو أكثر لطلب الوصول إليه.
- انقر على بدء العرض التجريبي.
- أكِّد أنّه يمكنك الموافقة على طلب ربط الحساب ورفضه عندما يُطلب منك ذلك.
- تأكَّد من إعادة توجيهك إلى منصّتك.
