概览
身份验证流程的目的是向付款集成商(集成商)识别用户身份和进行身份验证。
身份验证是对其他方法的输入。尤其是针对 associateAccount 和 capture。这意味着,身份验证证明将用作这两种方法的输入(参数)。
Google 还可以使用独立模式下的身份验证流程来验证用户。在这种情况下,它不用作任何其他流的输入,而只是验证用户是否能够对此身份进行身份验证。
请注意,在您上手使用时,Google 会与您一起选择最适合您的产品的身份验证机制。
该流程的运作方式
对用户进行身份验证的方法有两种,每种方法都有自己的流程。在集成时,集成商必须确定要使用哪一种。
- 重定向身份验证
- SMS-MT 动态密码身份验证
重定向身份验证
需要进行身份验证的 Google 用户可能会被重定向到集成商的应用或网站,要求其验证身份。下面简要介绍了此流程中的步骤:
- Google 将用户重定向到集成商的 Web 应用或 Android 应用,以便对用户进行身份验证。
- 为了进行身份验证,身份验证
requestId(来自AuthenticationRequest)会用作身份验证的证明。 - 这将产生一个名为
AuthenticationResponse的签名响应。 - 之后,应用或网站会将用户重定向回 Google。
重定向身份验证使用 HTTP GET 方法,并将参数编码到网络应用的网址中。它使用 Android intent 进行 Android 应用身份验证。如需详细了解编码,请参阅网络身份验证;如需了解 Android intent 参数,请参阅 Android 身份验证。
每种身份验证机制都会生成一个名为 AuthenticationResponse 的签名响应。此 intent 应包含经过加密和编码的 Google 标准付款身份验证响应 (gspAuthenticationResponse),以传达成功的身份验证。如果在独立模式下使用,则 gspResult 和签名用于确定是否成功通过身份验证。
以下序列图显示了用户的浏览器 Google 与集成商 Web 应用之间的交互:
重定向网页身份验证流程
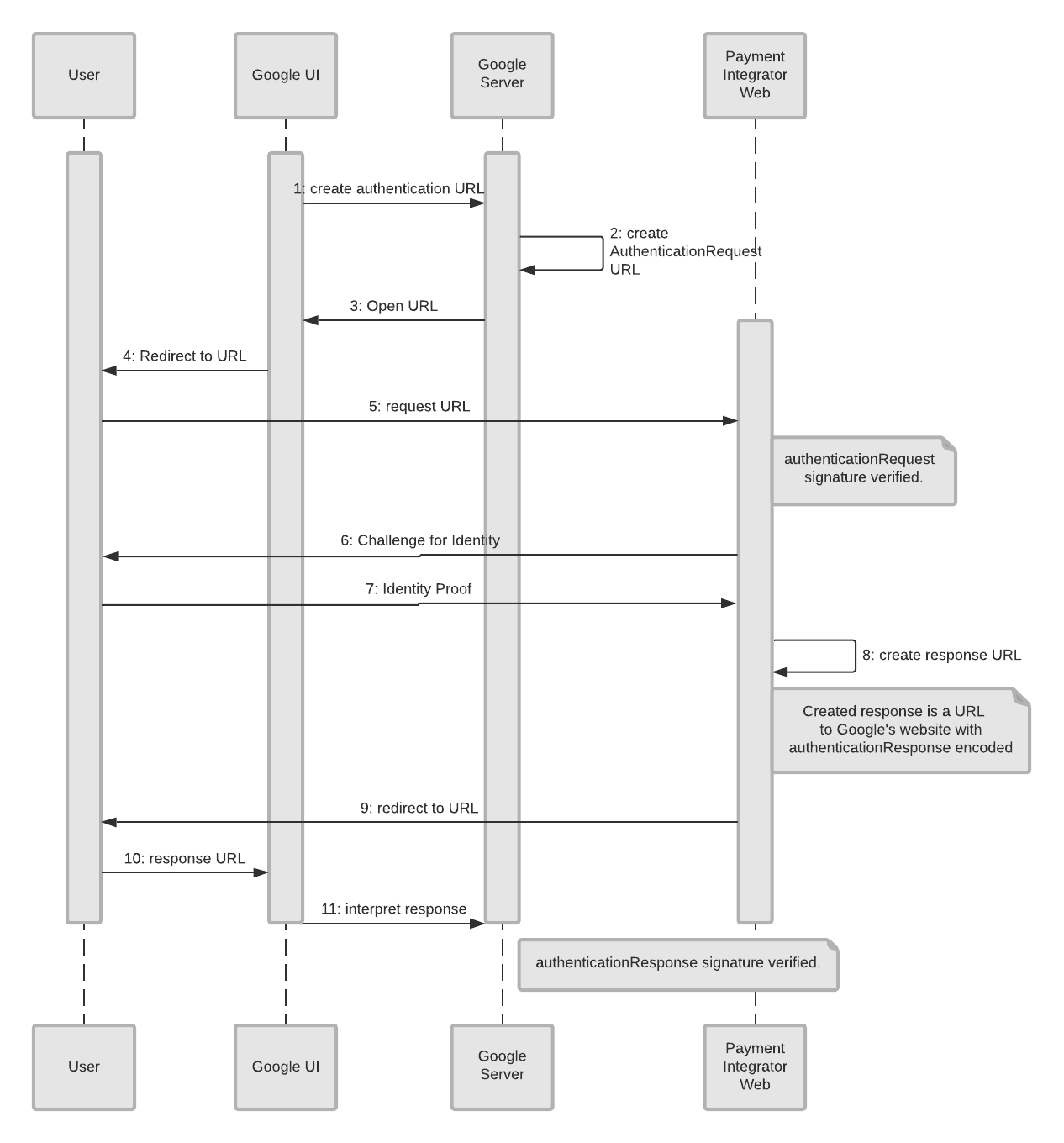
下面列出了这些对象及其所代表的含义:
- 用户:希望向其 Google 帐号添加付款方式的人。
- Google 界面:在本例中是 Google 的网页界面,客户从该界面中开始设置付款方式。
- Google 服务器:在 Google 上执行身份验证检查以及其他身份验证任务的后端服务器。
- 付款集成商网站:用户拥有帐号的集成商网站。
对于此身份验证流程,我们已假设用户位于 Google 的网站(Google 界面)并且正尝试添加付款方式。一切从这里开始。
- Google 界面会创建一个身份验证网址,该网址会发送到 Google 服务器(后端)。这会触发身份验证流程。
- Google 服务器创建身份验证请求 (
AuthenticationRequest)。 - 发送到 Google 界面的身份验证请求。
- 用户会收到提示,要求其向集成商验证其 ID。
- 用户回复称他们想要进行身份验证,系统将该消息发送到集成商的网站。
- 付款集成商的网站要求验证用户身份。
- 用户提供的身份证明将发送到付款集成商的网站。
- 集成商针对收到的证据创建响应 (
authenticationResponse)(在消息中编码authenticationResponse)。 - 此响应网址会发送给用户。
- 响应网址会立即从用户发送到 Google 界面。
- Google 界面会向 Google 服务器发送响应。
- Google 服务器将响应解读为已验证。
下一个序列图显示了用户的手机 Google 与集成商的 Android 应用之间的交互:
重定向 Android 应用身份验证流程
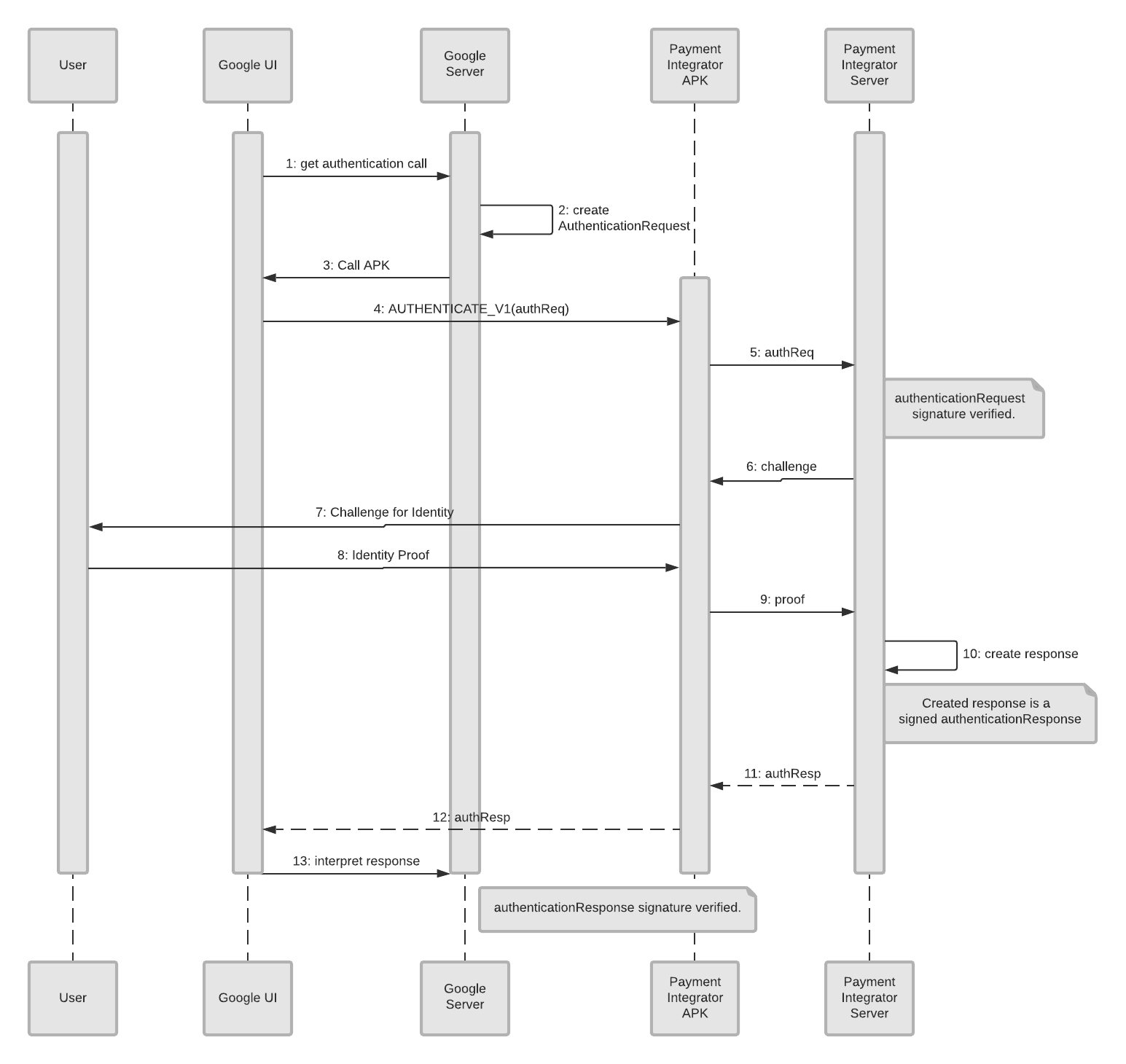
以下是这些对象及其所代表的含义:
- 用户:希望向其 Google 帐号添加付款方式的人。
- Google 界面:在本例中是应用界面,客户在该界面中开始设置付款方式。
- Google 服务器:在 Google 上执行身份验证检查以及其他身份验证任务的后端服务器。
- 付款集成商 APK:用户有权访问其集成商帐号的集成商应用。
- 付款集成商服务器:集成商的后端服务器,其中存储了用户的信息。
由于这是一个身份验证流程,因此我们假设用户使用的是某个应用(Google 界面),并正在尝试添加付款方式。初始化从这里开始。
- Google 界面会创建一个发送到 Google 服务器(后端)的身份验证调用。
- Google 服务器创建身份验证请求 (
AuthenticationRequest)。 - Google 服务器向 Google 界面(应用)发送调用 APK,请求身份验证。
- Google 界面会将用户信息发送到付款集成商 APK (
AUTHENTICATE_V1(authReq))。 - 付款集成商 APK 将请求 (
authReq) 发送到付款集成商的服务器。 - 付款集成商服务器将质询发回付款集成商 APK。
- 付款集成商 APK 将质询发回用户。
- 用户提供其身份证明,系统会将该证明发送到付款集成商 APK。
- 然后,此证明会发送给付款集成商服务器。
- 服务器会创建一个已签名的
authenticationResponse。 - 身份验证响应成功,并且系统向付款集成商 APK 发送一条
authResp消息。 - 成功消息 (
authResp) 将从付款集成商 APK 发送到 Google 界面。 - Google 界面会将响应发送到 Google 服务器。
- Google 服务器会解读成功响应。
SMS-MT 动态密码身份验证
另一种身份验证方法是短信服务、移动设备终止、动态密码 (SMS-MT OTP)。此机制利用用户的电话号码向用户发送用于身份验证的一次性密码。Google 要求集成商向用户的电话号码发送动态密码,在用户收到动态密码并将其输入到 Google 界面后,用户即会获得验证。
这包括以下步骤:
- Google 的界面 (UI) 会提示用户输入已在集成商处注册的电话号码。
- 用户在 Google 界面中输入电话号码。
- Google 触发集成商(调用
sendOtp方法)向用户发送动态密码 (OTP)。 - 用户收到包含动态密码的短信。
- 然后,用户需要将收到的动态密码(用于
capture、associateAccount和verifyOtp的输入)输入 Google 界面,以对用户进行身份验证。这是身份验证证明。
在独立模式下,系统只会调用 verifyOtp 方法来验证动态密码值。
以下序列图显示了发送动态密码时用户电话、Google 和集成商之间的互动:
电话(发送动态密码)身份验证流程
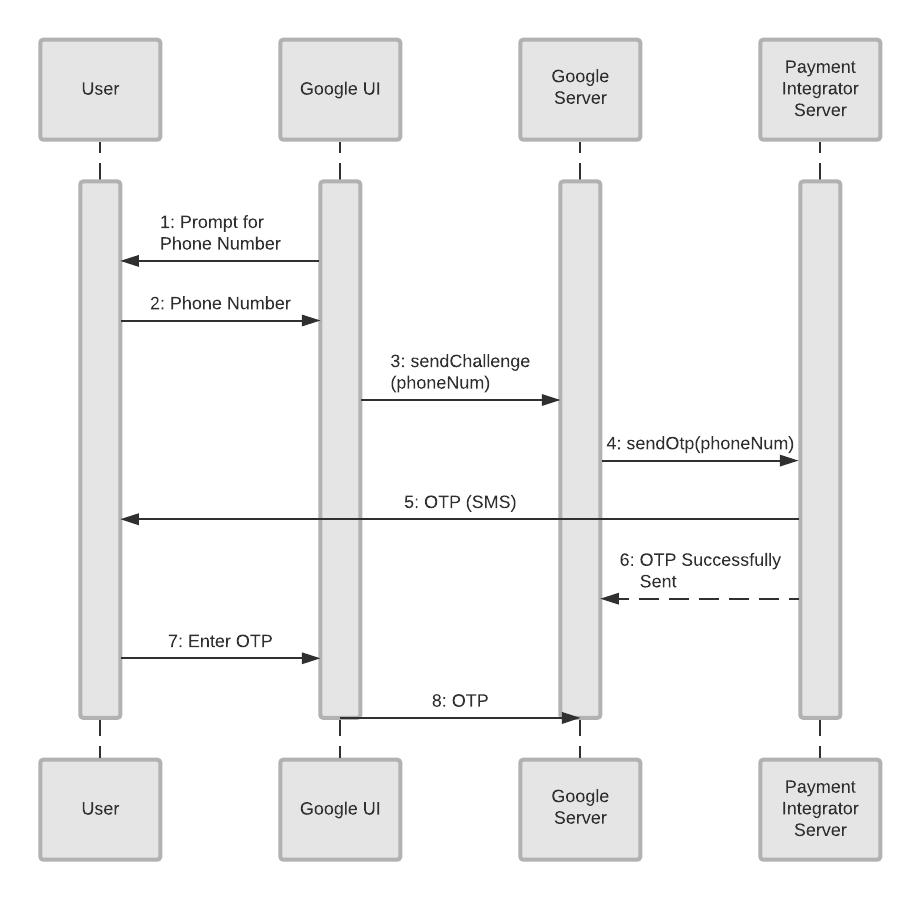
下面列出了图表中的各个对象及其所代表的含义:
- 用户:希望向其 Google 帐号添加付款方式的人。
- Google 界面:在本例中显示的是客户开始设置付款方式的 Google 网站或手机应用。 注意:如果 Google 界面是一个手机应用,则会跳过前几个步骤,因为手机已经知道用户的电话号码。
- Google 服务器:在 Google 上执行身份验证检查以及其他身份验证任务的后端服务器。
- 付款集成商服务器:集成商的后端服务器,其中存储了用户的信息。
由于这是动态密码身份验证流程,因此我们已假定用户位于 Google 手机应用或网站(Google 界面)中,并正在尝试添加付款方式。初始化从这里开始。
- Google 界面(电话或网站)会提示用户输入电话号码。
- 用户在 Google 界面中输入其电话号码。
- Google 界面会将该号码 (
sendChallenge(phoneNum)) 发送到 Google 服务器。 - Google 服务器向付款集成商服务器 (
SendOtp(phoneNum)) 发送请求,以便发送动态密码。 - 付款集成商服务器向用户发送动态密码 (OTP)。
- 付款集成商服务器在第 5 步中响应 Google 的请求,表明动态密码已成功发送。
- 用户在 Google 界面(手机或网站)中输入此动态密码。
- Google 界面会将动态密码发送到 Google 服务器,该密码最终会发送给付款集成商进行验证。此操作将验证用户的身份和对用户的身份。
身份验证和重新验证
可以在两个时间点进行身份验证:
- 初始身份验证 - 用于对用户进行身份验证。初始身份验证用作
associateAccount方法的输入。 - 重新验证 - 在所有其他情境中使用,例如独立验证或用作
capture的输入。
重新身份验证不同于初始身份验证。它绝不会希望重新识别用户身份,只是为了重新进行身份验证。Google 会使用重新验证机制来要求用户验证自己拥有特定的帐号,具体的操作由 Google 自行决定。
在此过程中,系统会向原始关联(来自关联流程)提供一项名为 associationId 的引用。这是在关联流程中调用 associateAccount 方法提供的。associationId 确定要质询的帐号。为安全起见,用户必须无法更改要验证的帐号。
对于短信 MT 动态密码重新身份验证,Google 会将最初调用 sendOtp 时提供的电话号码保存为固定号码。同样,出于安全考虑,此 ID 无法更改。
以下示例流程说明了 Google 决定在购买之前质询(重新进行身份验证)的情况:
重新进行身份验证流程
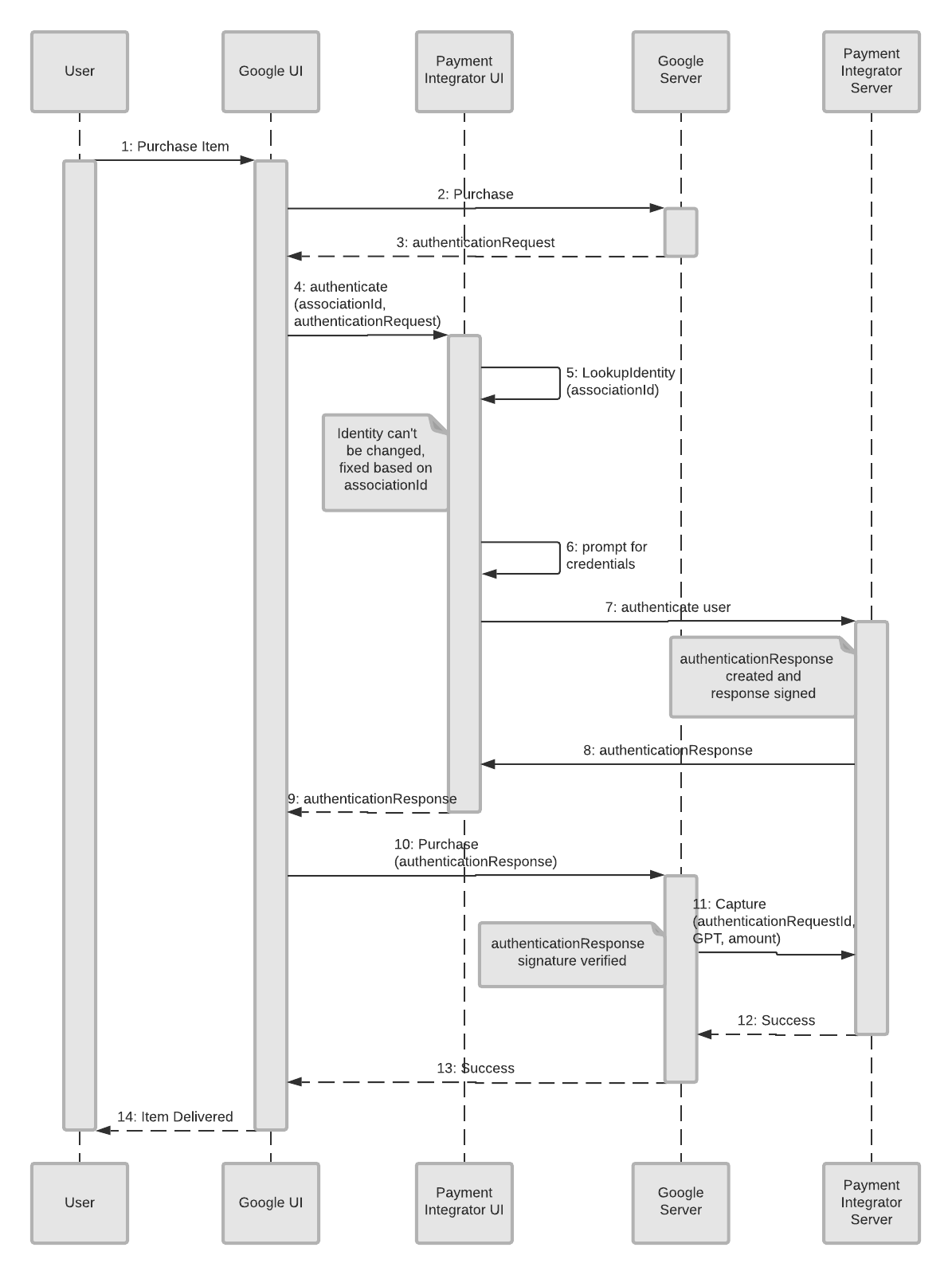
对象列表及其所代表的含义如下:
- 用户:希望进行购买的用户。
- Google 界面:在本例中是用户开始购物的 Google 网站或手机应用。
- 付款集成商界面:面向客户的网站或应用,用户可通过集成商访问其帐号信息。
- Google 服务器:在 Google 上执行重新身份验证检查以及其他任务的后端服务器。
- 付款集成商服务器:集成商的后端服务器,其中存储了用户的信息。
重新进行身份验证流程从客户开始购物时开始。这会初始化一个流程,以重新验证用户身份。
- 用户决定购买商品或服务。
- 请求会从 Google 界面发送到 Google 服务器。
- Google 服务器会向 Google 界面发回身份验证请求 (
authenticationRequest)。 - Google 界面会向付款集成商界面发送请求,以便对用户进行身份验证(
associationId、authenticationRequest)。 - 付款集成商界面将查找用户以验证其身份 (
LookupIdentity(associationId))。 - 付款集成商界面会在界面(集成商的网站或应用)上提示用户输入凭据。
- 身份验证响应将发送到付款集成商服务器。
- 已签名的身份验证响应 (
authenticationResponse) 发送回付款集成商界面。 - 身份验证响应 (
authenticationResponse) 从付款集成商界面发送到 Google 界面。 - Google 界面将包含购买信息的响应发送到 Google 服务器。
- Google 服务器向付款集成商服务器(
authenticationRequestId、GPT、金额)发送capture消息(以查找可用资金)。 - 付款集成商服务器将成功消息发送回 Google 服务器。
- Google 服务器向 Google 界面发送成功消息。
- Google 界面将商品递送给客户(或通知他们商品很快就会送达)。
SMS-MO 身份验证
短信服务(移动源身份验证流程)利用包含身份验证请求 ID 的短信(从用户手机发送到付款集成商)对用户进行身份验证。
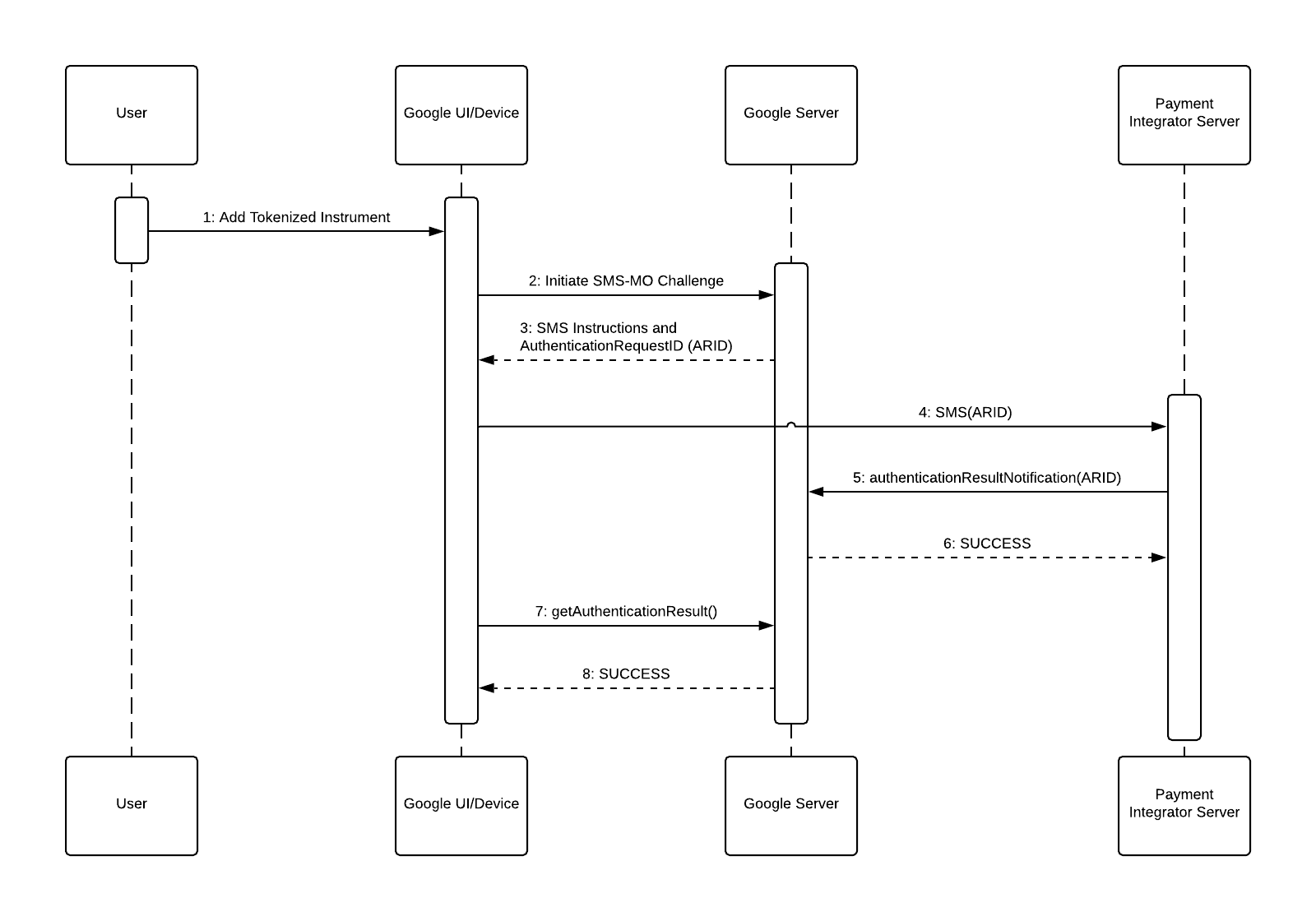
下面列出了图表中的各个对象及其所代表的含义:
- 用户:希望向其 Google 帐号添加付款方式的人。
- Google 界面/设备:在本例中是 Google 手机应用,客户可以开始设置付款方式。
- Google 服务器:Google 的后端服务器,可根据身份验证请求 ID (ARID) 生成短信指令,并接收集成商提供的身份验证结果。
- 付款集成商服务器:集成商的后端服务器,用于接收身份验证短信并将身份验证请求 ID 返回给 Google。
由于这是一个身份验证流程,因此我们假设用户使用的是某个应用(Google 界面),并正在尝试添加付款方式。初始化从这里开始。
- 用户选择要添加的代币化付款方式。
- Google 界面调用 Google 服务器以启动 SMS-MO 验证。
- Google 服务器返回 SMS 指令,其中包含目标和包含身份验证请求 ID 的正文。
- Google 界面会向付款集成商发送短信。
- 付款集成商服务器使用身份验证请求 ID 调用 Google 服务器上的 authenticationResultNotification 端点。
- 身份验证请求 ID 由响应 SUCCESS 的 Google 服务器验证。
- Google 界面调用 Google 服务器以获取身份验证尝试的结果。
- Google 服务器响应 SUCCESS。
模拟 SMS-MO 身份验证
为了对 SMS-MO 身份验证流程执行诊断测试,Google 定义了一个模拟短信端点。这样,在沙盒环境中执行测试关联时,就无需发送并验证真正的短信。
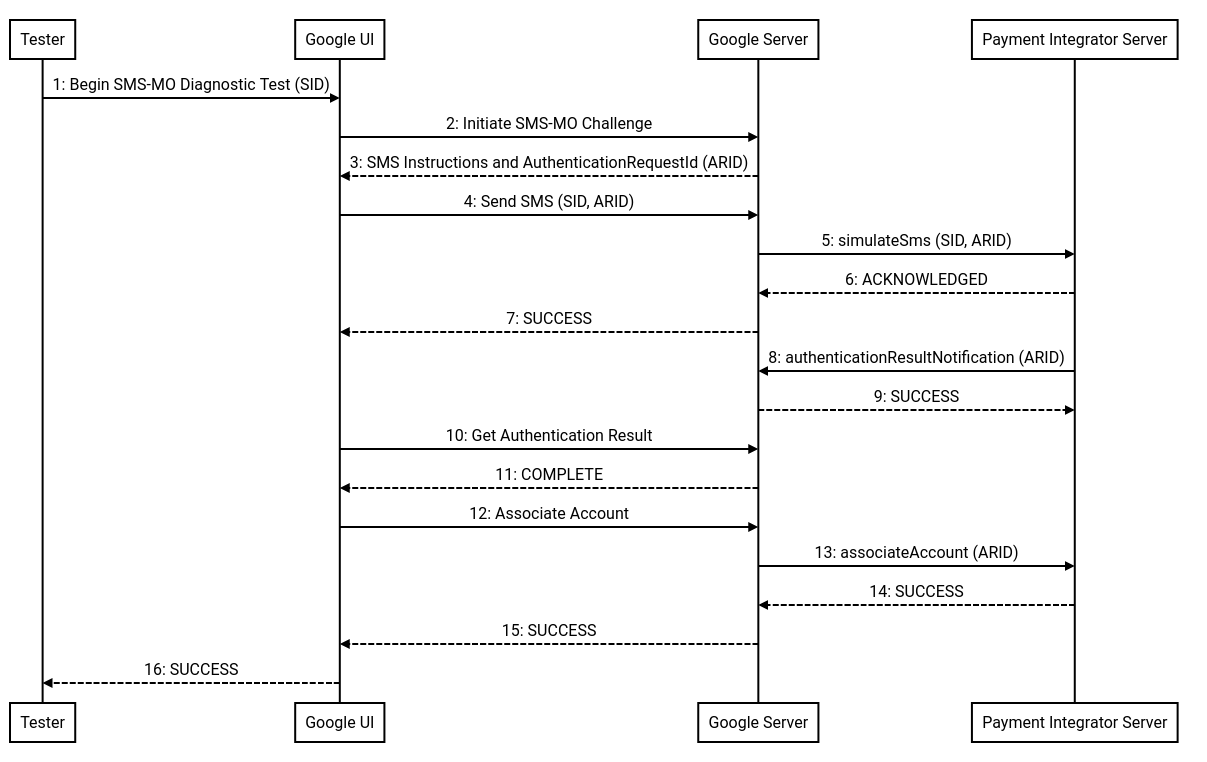
下面列出了图表中的各个对象及其所代表的含义:
- 测试人员:发起短信-MO 关联诊断测试的人员。
- Google 界面:测试人员在此界面中开始并监控 SMS-MO 诊断测试的状态。
- Google 服务器:Google 的后端服务器,用于生成带有身份验证请求 ID (ARID) 的短信指令、发送模拟短信,并接收集成商提供的身份验证结果。
- 付款集成商服务器:集成商的后端服务器,用于接收模拟身份验证短信并向 Google 返回身份验证请求 ID。
此流程中的步骤如下:
- 测试人员通过提供用于测试的测试用户 ID (SID),开始 SMS-MO 诊断测试。此 SID 将包含在对付款集成商的
simulateSms调用中。 - Google 界面调用 Google 服务器以启动 SMS-MO 验证。
- Google 服务器返回 SMS 指令,其中包含目标和包含身份验证请求 ID 的正文。在此测试中,目标将被付款集成商的沙盒 HTTPS 连接覆盖。
- Google 界面调用 Google 服务器来发送模拟短信。
simulateSms从 Google 服务器到付款集成商服务器进行调用。API 调用中包含身份验证请求 ID 和订阅者 ID(如第 1 步所述)。- 付款集成商服务器响应 ACKNOWLEDGED。
- Google 服务器对 Google 界面做出响应 SUCCESS。
- 付款集成商服务器使用身份验证请求 ID 调用 Google 服务器上的 authenticationResultNotification 端点。
- Google 服务器响应 SUCCESS。
- Google 界面调用 Google 服务器以获取身份验证尝试的结果。
- Google 服务器响应 COMPLETED。
- Google 界面调用 Google 服务器以执行关联尝试。
associateAccount从 Google 服务器到付款集成商服务器进行调用。- 付款集成商服务器响应“SUCCESS”。
- Google 服务器响应 SUCCESS。
- Google 界面会更新,以向测试人员表明 SMS-MO 诊断测试已成功完成。
最佳实践和其他注意事项
平台选择
通过提供移动应用和桌面 Web 身份验证流程,集成商可以覆盖尽可能多的用户。Google 强烈建议集成商支持 Android 应用,因为这样可以提供最佳的用户体验,从而获得最高的转化率。在 Web 应用和 Android 应用的身份验证 API 中传递的参数相同。
