บทนำ
บาร์โค้ดแบบหมุนเวียนก็เหมือนกับบาร์โค้ดทั่วไป แต่จะเปลี่ยนแปลงเป็นระยะๆ โดยปกติทุกนาที และเทอร์มินัล/เครื่องอ่านจะถูกตั้งโปรแกรมให้ยอมรับ อันล่าสุด มาตรการรักษาความปลอดภัยนี้จะช่วยลดความเสี่ยงที่เกี่ยวข้องกับ การจับภาพหน้าจอบาร์โค้ด โดยเฉพาะการขโมยตั๋วหรือตั๋วที่ไม่ได้รับอนุญาต การขายต่อ บาร์โค้ดแบบหมุนยังสามารถทำหน้าที่เป็นตัวเลือกสำรองสำหรับอุปกรณ์ที่ไม่สามารถ ใช้ประโยชน์จากการแตะอัจฉริยะเนื่องจากไม่สนับสนุน NFC (ไม่มีฮาร์ดแวร์ หรือ ปิดใช้งานซอฟต์แวร์)
เอกสารอ้างอิง API
สำหรับรายละเอียดทางเทคนิคเกี่ยวกับการหมุนบาร์โค้ด โปรดดูที่
RotatingBarcode ประเภท
ตัวอย่างเพย์โหลด
| JSON | |
|---|---|
{ "rotatingBarcode": { "type": "QR_CODE", "valuePattern": "MyRotatingBarcode-{totp_timestamp_seconds}-{totp_value_0}", "alternateText": "Ticket#: 1234567890", "totpDetails": { "algorithm": "TOTP_SHA1", "periodMillis": "3000", "parameters": [ { "key": "3132333435363738393031323334353637383930", "valueLength": "8" } ] } } } |
|
กลไกสำรอง
ในอุปกรณ์ของผู้ใช้ ระบบจะใช้กลไกการแลกสิทธิ์เพียง 1 รายการในช่วงเวลาหนึ่ง ทั้งนี้ขึ้นอยู่กับการกำหนดค่าบัตรและความสามารถของอุปกรณ์ ระบบจะใช้ประเภทการแลกสิทธิ์ต่อไปนี้ตามลำดับความสำคัญ
-
การแตะอัจฉริยะ: หากมีการระบุเพย์โหลดการแตะอัจฉริยะไว้ และหากอุปกรณ์รองรับ
NFC/HCE
- โปรดทราบว่าผู้ใช้จะลบล้างได้ด้วยการคลิก "แสดงโค้ด" จะบังคับให้แสดงบาร์โค้ด/บาร์โค้ดแบบคงที่ที่หมุน
- บาร์โค้ดแบบหมุน: หากระบุเพย์โหลดบาร์โค้ดแบบหมุน
- บาร์โค้ดแบบคงที่: หากระบุเพย์โหลดบาร์โค้ดไว้
การระบุเพย์โหลดการแลกสิทธิ์หลายรายการช่วยให้มั่นใจได้ว่าจะมีการรองรับผู้ใช้ทุกคน อาจมีผลกระทบต่อความปลอดภัย โดยเฉพาะอย่างยิ่ง การใช้บาร์โค้ดแบบคงที่เป็น การใช้บาร์โค้ดแบบหมุนทำให้ประโยชน์ด้านความปลอดภัยส่วนใหญ่ของการใช้ การหมุนเวียนบาร์โค้ด สำรองบาร์โค้ดแบบคงที่จะแสดงในมุมมองเว็บเท่านั้น หรือไคลเอ็นต์ที่ไม่รองรับบาร์โค้ดแบบหมุน ตั้งแต่วันนี้เป็นต้นไป เราคาดว่า ไคลเอ็นต์ทั้งหมดของ Google Wallet เพื่อรองรับบาร์โค้ดแบบหมุน
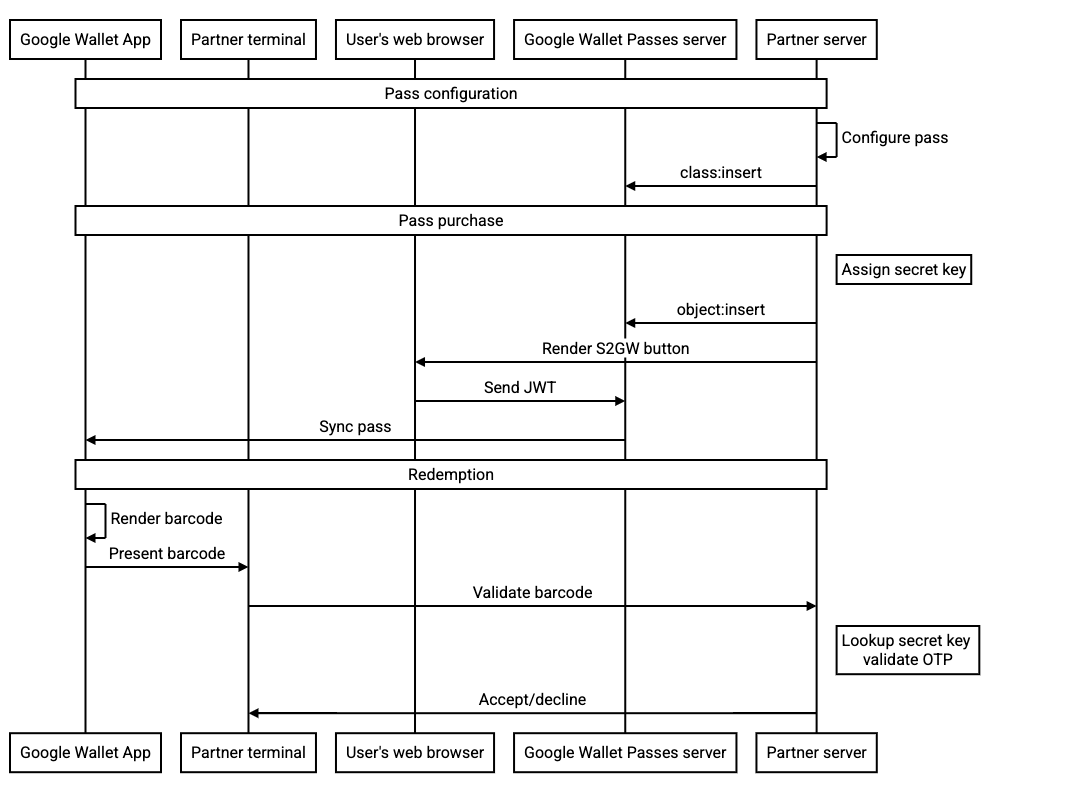
บันทึกโฟลว์
Google Wallet API มีขั้นตอนดำเนินการหลายวิธี ดังนี้
- สร้างชั้นเรียนทั่วไปเมื่อประหยัดเวลาหรือล่วงหน้า
- ส่งวัตถุที่สมบูรณ์ใน JWT หรือบันทึกวัตถุล่วงหน้า แล้วอ้างอิงตามรหัสใน JWT
- อัปเดตออบเจ็กต์หลังจากที่บันทึกแล้ว
ฟิลด์ RotatingBarcode ที่เสนอใช้ได้กับขั้นตอนเหล่านี้ทั้งหมด แต่เพื่อปรับปรุงความปลอดภัย เราขอแนะนำการดำเนินการดังต่อไปนี้
-
เรียกใช้
object:insertAPI เพื่อแทรกบัตรลงใน เซิร์ฟเวอร์ Google Wallet และกำหนดค่าปุ่ม "เพิ่มลงใน Google Wallet" เป็น อ้างอิงออบเจ็กต์ที่เฉพาะเจาะจงตามรหัสใน JWT ซึ่งช่วยให้มั่นใจว่า JWT ที่ได้จะไม่มีคีย์ลับของบาร์โค้ดแบบหมุน - ใช้คีย์ลับ OTP ที่กำหนดขอบเขตเป็นบัตรเดียว
- คีย์ เว้นแต่จะมีการอัปเดต คีย์ควรมีอายุการใช้งานของ ข้ามประเทศ เราไม่คิดว่าจะมีการอัปเดตคีย์นี้ในระดับความถี่ใดก็ตามในระหว่าง ซึ่งเป็นการดำเนินการตามปกติ
แผนภาพลำดับต่อไปนี้แสดงการไหลเวียนระหว่างนักแสดงต่างๆ สำหรับการผสานรวมทั่วไป: